10 Best Ways to Protect Images Online

Have you shared a stunning photo lately? Don’t let your hard work get stolen.
Protecting your digital images is doable through simple measures outlined here. You can learn how to protect images online and secure image content with these tricks.
We’ll overview platform protections, preemptive watermarking, and even formal copyright registration—little moves that prevent unauthorized usage or theft of your images.
The goal is to balance visibility with locked-down ownership rights. These pro tips help your work stand out reliably while granting you peace of mind once photos are published.
Quick Takeaways
- Safeguard your photos from unauthorized use with techniques like copyright registration, visible watermarks, and metadata embedding.
- Use tools like reverse image search or copy-tracking software to spot and address image misuse online.
- Limit full-resolution sharing, disable embedding, and use on-screen watermarks to deter theft without sacrificing visibility.
Why Protect Images Online?
Sharing your photos online is exhilarating but also risky. Your hard-earned images could easily be misused on ads or products without your consent.
This loses control of how your work spreads. So before posting that great shot, it pays to explore simple yet intelligent options for securing your artistry.
Here’s why image protection matters:
1. Protect your legal rights: Posting images online allows others to easily copy and use them without permission, violating your creative rights. You can protect images via watermarking and registration to establish ownership, deter infringement, and retain control over how images are used.
2. Preserve commercial value: Your images have inherent commercial value both presently and for future licensing opportunities. Safeguarding them protects your ability to benefit financially from your work.
3. Maintain creative reputation: As an artist, a body of work shows your style and abilities. Unauthorized use that alters perception harms your creative reputation. Visible watermarks prevent your name from appearing on out-of-context images.
4. Gain recourse for violations: Registering and visibly watermarking images proves you created the work, providing grounds to demand removal or sue for damages if stolen. Deterrent markings also discourage misuse in the first place, making your work less attractive to infringers.
5. Avoid penalties: You risk legal allegations and penalties if someone else registers your image first. Consistently marking originals with watermarks and registering early prevents loss of control over your creations.
The 10 Best Ways to Protect Images Online
While there’s no foolproof way to prevent infringers from copying your images. However, learning a few simple methods on how to protect photos can significantly lower the chances.
Following an approach with different strategies is ideal for ultimate protection.
1. Register Copyright
Copyright, in a basic sense, means “right to copy.” Generally, any person who creates an image holds exclusive rights to the copy. But anyone can still lay claim to your images.
Register your photos with the U.S. Copyright Office to establish stronger legal protection. Doing so creates a public record documenting your ownership, including the dates you created the images.
How to Copyright Images
The process of registering a copyright is pretty straightforward. You start by filling out an application, paying a fee, and then submitting digital copies of your photos.
There’s also an option to submit paper copies of your original creations.
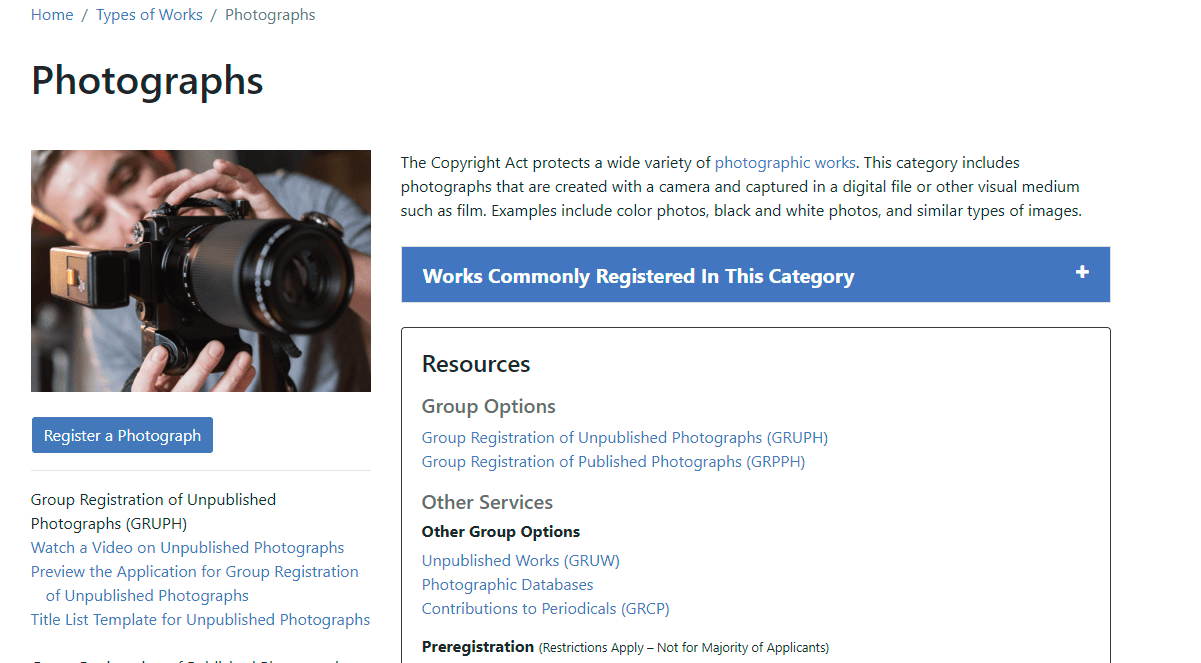
Before you can fill out the application form, register an account with the U.S. Copyright Office using this link.
You must create a user ID and set a password to access the system. Once done, log in to your account.
This fee is usually nonrefundable, and the charges are subject to change. You can use your credit or debit card to pay.
Once done, deposit a copy of your work to become part of public records. The deposit requirements vary based on the following:
- Whether the photos were published or unpublished
- If published, was it inside or outside the United States?
If the photos are available online, submit copies of them.
Why You Should Register Image Copyright
Registration provides essential rights if you press charges over copyright infringement.
Successful petitions may yield statutory fines of $750-$30,000 per infringed work. However, to qualify, photographs must be registered before a violation occurs or within three months of online publication. Later registration is invalid for damage claims.
Many photographers assume automatic copyright protection upon capturing an image. However, pre-registration establishes stronger legal recourse.
Besides pressing lawsuits, you can enforce a DMCA takedown with a registered photograph.
DMCA notices provide an out-of-court route requesting infringing websites through their hosting platforms to remove copied images.
While copyright registration is helpful, it limits transformative fair use of your creative work.
Fair use prohibits copyright infringement for commentary, news reporting, teaching, criticism, scholarship, and research.
Given the use cases, additional preventive measures like watermarking warrant consideration.
How to Monitor the Use of Copyright Images
Although copyright registration effectively prevents unauthorized use, monitoring where your images are displayed online is also important.
The best part is you don’t need premium software to do this. Here are the steps to follow:
Step 1. Use Google Images to conduct reverse image searches.
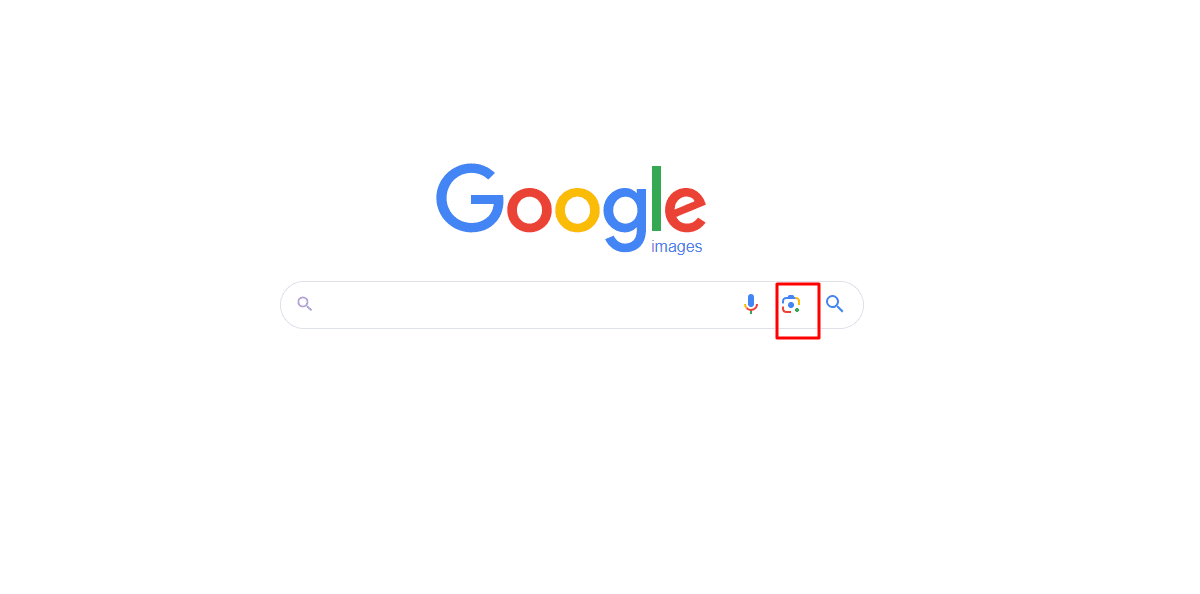
Step 2. Upload the image, enter the URL, and scan the web for results.
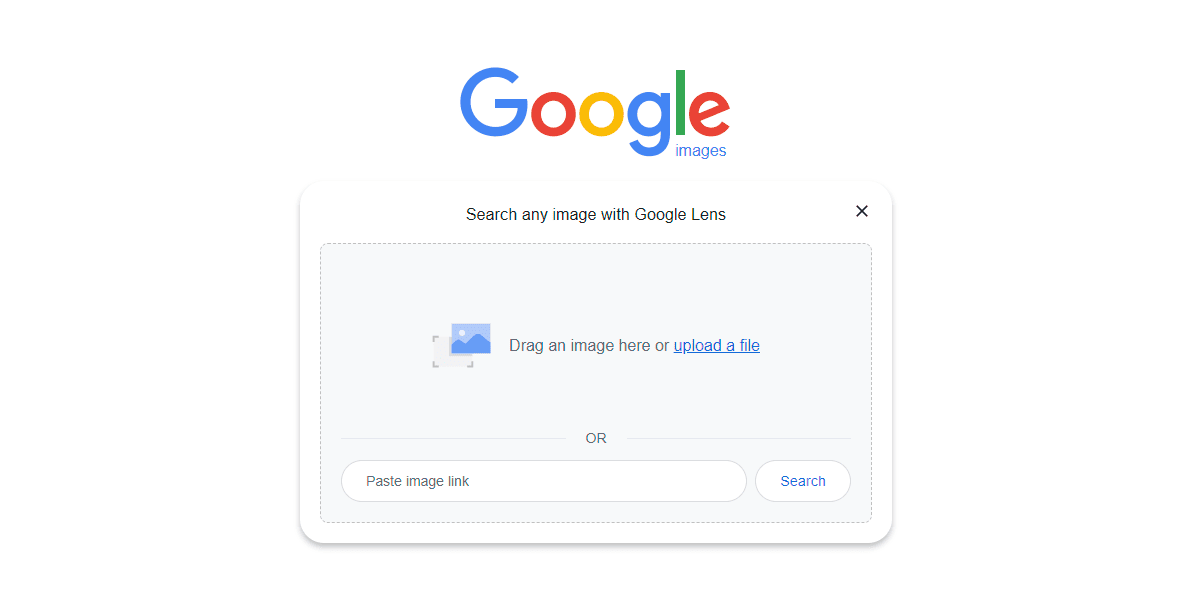
3. Any exact matches will appear in your search results so you can assess if the publisher acquired a license or if it’s a potential infringement.
Alternatively, copy-tracking tools like Digimarc embed undetectable watermarks into images.
The tool continuously scans for the use of your marked images across different websites. Most services demand you pay a subscription to automate discovery.
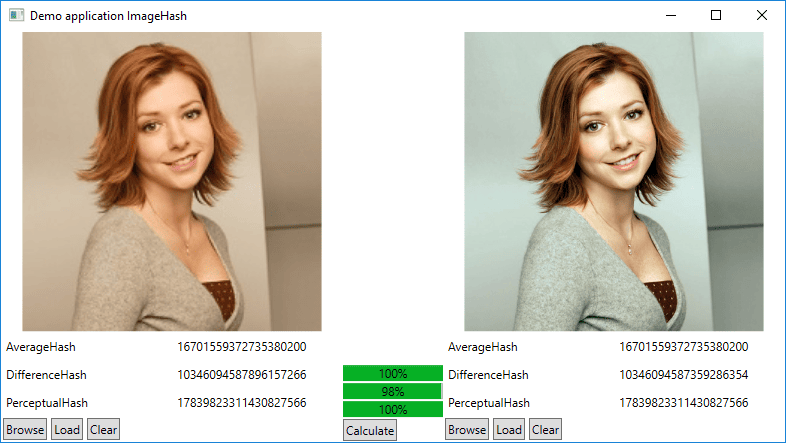
2. Image Hashing
Image hashing is a mathematical computation that transforms photos into unique strings of code called hash values.
Digital copies of an original image all have the same hash value. Photographers refer to hash values as “digital fingerprints.”
Generally, every image has a grid of colored dots called pixels. Image hashing algorithms scan and convert these pixels, assigning them numerical values.
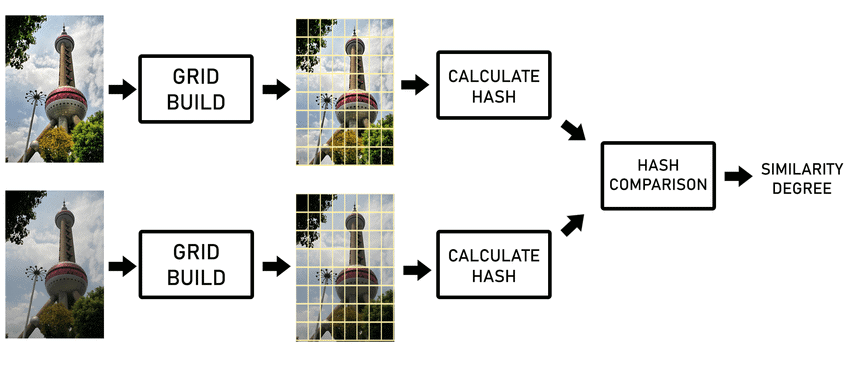
These numerical values represent the brightness and color of each pixel. The alphanumeric strings generated are much easier to query at high speeds.
Any change to the image, including minor edits like filters and cropping, produces different hashes. It’s similar to an image’s barcode, sensitive to even the slightest alterations.
There are two main image-hashing techniques:
- Perceptual hashing
- Difference hashing
Perceptual Hashing
Perceptual hashing analyzes images in a way our eyes and brains would. It looks at the overall visual impact – not just pixel differences. So it can detect when photos are alike, even with small tweaks.
The technique checks into an image’s frequencies and patterns. Kind of like how we focus on shapes and spatial relationships rather than examining every tiny detail.
So, while two pics may vary pixel by pixel, perceptual hashing spots if they’re strikingly similar. That allows the detection of copies other methods would miss.
The most utilized image hashing solution is PhotoDNA. The technology identifies near-duplicate copyright-protected images.
Benefits of perceptual hashing include:
- Improved efficiency since it requires fewer computational resources. Comparisons are also faster.
- Minimized false positive matches.
- Minor edits often preserve the perceptual fingerprint.
However, while sophisticated, perceptual hashing has limitations:
- If an altered image no longer matches the original hash, the modifications cannot be pinpointed.
- Identical appearing images can produce different hashes when converted from JPEG to PNG.
- Carefully engineered noise additions can alter image contents while evading detection.
Difference Hashing
Difference hashing algorithms evaluate pixel arrangements within images in detail. They divide images into blocks first and then compare localized pixel distributions between sections.
A common different hashing technique is “dHash.” It detects duplicate or near-identical photos by pinpointing matching structural pixel patterns across image blocks.
While excellent at identifying unmodified copies, difference hashes alter significantly with minor edits. As the method examines intricate pixel layouts closely, small position or orientation shifts can reshape hashes substantially.
Here’s a classic representation of difference hashing.
Combining hashing with digital watermarking helps overcome the limitations of perceptual and difference hashing.
Unique watermarks inserted into original image copies remain consistent even in modified copies.
When matches surface, image owners can review them to check if they infringe on copyright and issue DMCA takedowns.
Since different pics can share “fingerprints” sometimes, reviewing matches first-hand is key before accusing a website of copyright infringement.
While not as definitive, hashing helps earmark images online for further investigation.
3. Limit Image Access
Sharing full-resolution images online can be risky. You might aim to show off your skills, but websites and social media make it easy for anyone to steal and share your photos.
Sure, some might hesitate because of copyright, but many others might not even know or care. It’s best not to assume respect for your work. There are ways to make it harder, though.
Websites can use “right-click protection,” and some platforms offer download restrictions. But an unscrupulous user can still just take a screenshot. Legal agreements can help too, but their power is limited online.
The most optimal approach entails multilayered protections, including:
- Visible watermarking
- Using platform protection tools
- Requiring signed usage agreements
- Lowering image resolution
4. Send DMCA Takedown Notices
The Digital Millennium Copyright Act (DMCA) lets copyright holders get bootleg copies yanked from websites.
First, flag the pirated content’s URL and confirm you took the shot by noting the original dates plus any copyright certificates.
Draft the takedown clearly demanding they pull your stolen stuff. Remember to include your name and contact details.
The tricky part is usually tracking down host details. Start by searching the site’s hosting provider with free tools like Hosting Checker.
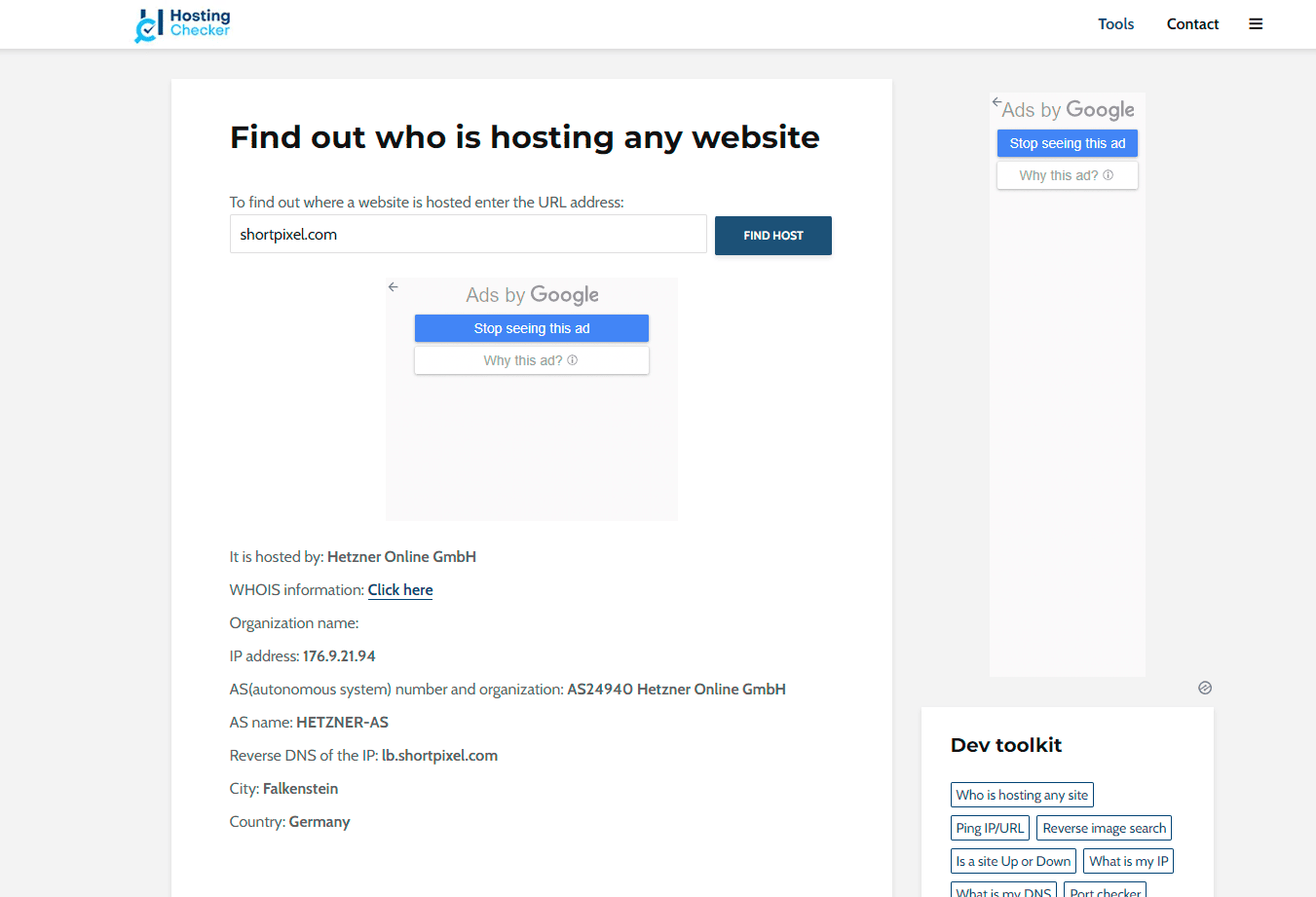
Reporting stolen content can be a bumpy road. Luckily, many websites offer DMCA takedown forms to streamline the process.
Even without a form, the U.S. Copyright Office website provides contact details for sending takedown notices directly. However, swift removal isn’t always assured. Website owners can challenge your request with counter-notices.
Legal action might be necessary for widespread commercial copyright infringement. Though lawsuits offer stronger solutions, they’re pricey and complex.
The high costs can be a deterrent, so we recommend a thorough review before filing claims to prevent false accusations.
5. Use Social Media Protection Tools
While sharing your work on social media can be thrilling, worries about ownership and unauthorized use are real. Your images could be widely shared without your permission or credit.
Thankfully, technology offers some protection against unauthorized copying. Platforms like Facebook and Instagram, which are part of the Meta ecosystem, use Meta Rights Manager.
This tool helps identify unauthorized shares and lets you set personalized restrictions on each post, like disabling downloads and embeddings.
Below are steps to follow to protect photo content on social media using Meta Rights Manager.
- Create or use an existing page (Facebook). Private pages are also eligible for this feature.
- Request access to the Rights Manager by filling out the application form. Here, you’ll also understand the scope of Meta Rights Manager.
- Wait for the application processing to complete. Meta will grant you access if you meet the outlined criteria.
- On approval, you’ll receive a tailored toolset to manage your content.
While this approach offers proactive infringement detection, false positives/negatives are inevitable.
First, register important images to facilitate swift DMCA takedowns, then utilize social media protection tools.
6. Add Metadata
Metadata is the information that describes an image beside the actual visual content.
Subtly embedding key metadata directly into photo files adds another layer of ownership confirmation. Metadata can include small details on the creation rights, licenses, contacts, and context.
This data remains with images when saved and shared online. If you use your phone to capture moments, the metadata includes EXIF data and IPTC details.
EXIF data comes directly from your camera and captures information like aperture, shutter speed, date and time, and the focal length.
Other details that strengthen metadata attribution include:
- Registration IDs
- GUIDs
- Model releases
- GPS data
- Software used
- Custom fields
Embedding an image with customized metadata makes it difficult for infringers to claim ownership. You can use Windows OS to add metadata to your image.
Simply right-click the image, then go to the “properties” section.
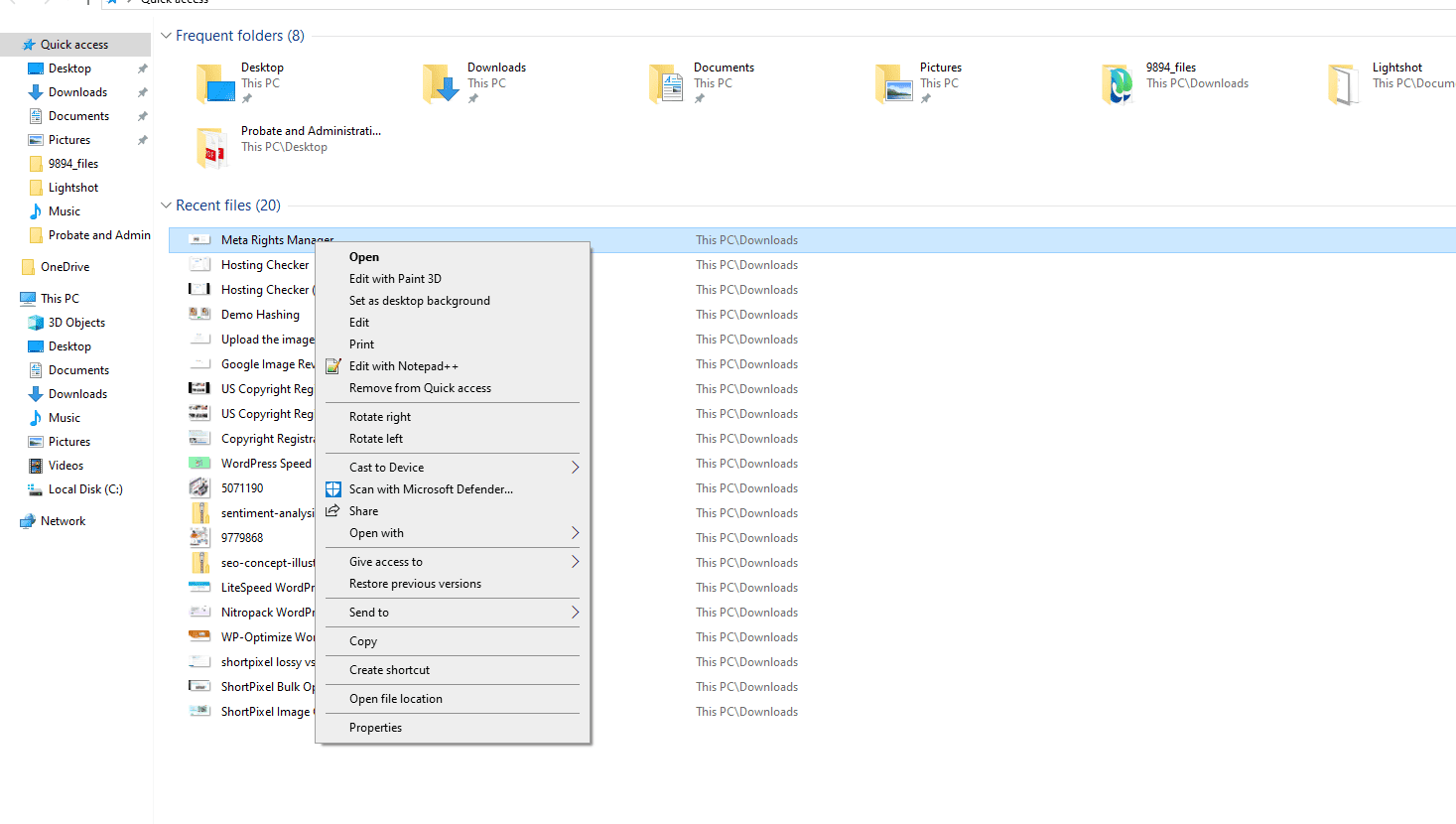
Navigate to the “Details” section and add the necessary information.
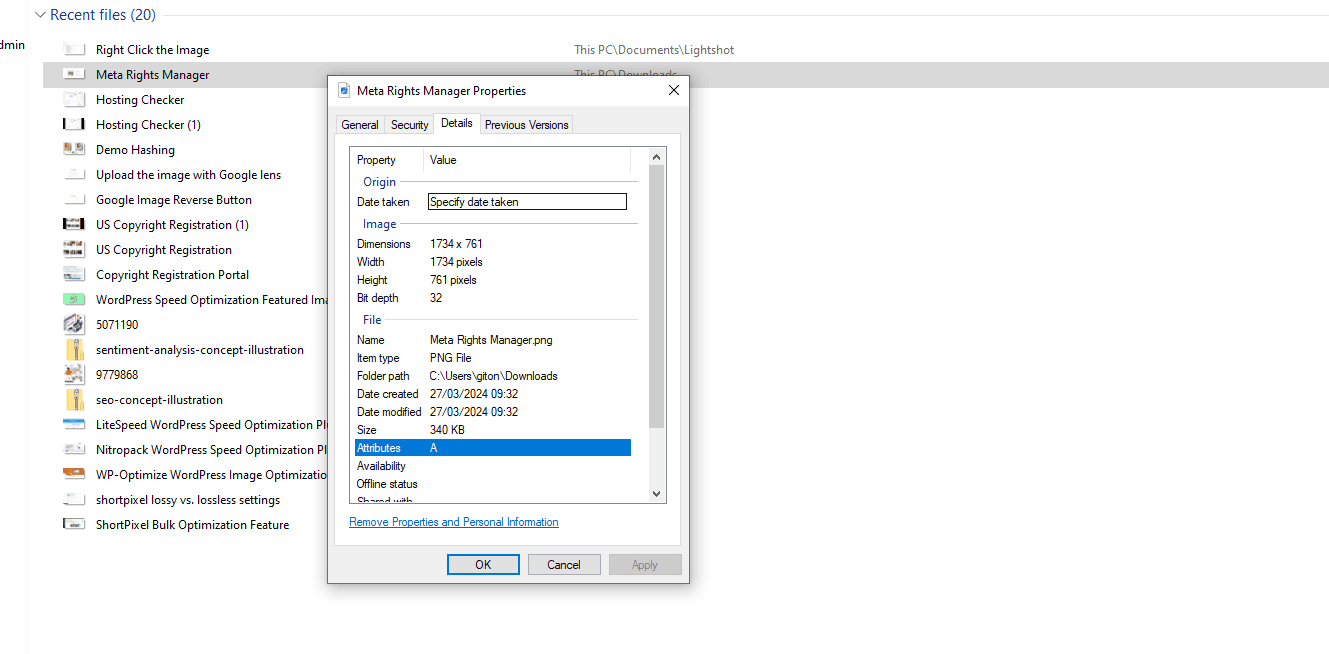
Editing image details is pretty easy. Just hit “Apply” to lock in your changes. Be mindful, though, especially if privacy is a concern.
Adding things like specific location data (GPS) might not be ideal for everyone. Thankfully, adding metadata is quite simple. Some cameras even let you customize the EXIF data they capture.
For even more control, photo editing software allows adding, editing, and managing various metadata formats. On top of that, platforms like Flickr offer IPTC data editing capabilities.
7. Disable Embedding
Image embedding allows third parties to integrate your photos directly into their websites or apps without permission. For example, someone could embed a tweet with your image into their blog, displaying it via links to your servers’ files.
Disabling embedding functionality provides a way to protect picture content online. Different platforms have their methods for restricting this capability. For instance, Instagram users can head to their profile settings and toggle the “Allow embeds” option off.
Facebook prevents embeddings by changing the privacy setting from public to friends-only for a given post. X platform users can disable photo tagging, making it harder for infringers to embed images through a tagged post.
8. Disable Right-Click Saving
Many website owners disable image right-clicking to halt unauthorized downloading.
While it’s a valid option, it doesn’t fully protect pictures. Disabling right-click functionality only helps with casual visitors.
Anyone dedicated to stealing your images can use, for example, the screenshot feature on their phones. Plus, blocking right-clicking can negatively impact image indexing and search engine performance.
How to Protect Images on Website by Disabling Right-Click on Images
Social platforms lack built-in right-click controls. Options only exist for individual websites:
- HTML code: Modify the <img> attribute to include the oncontextmenu= “return false;” attribute. Doing so prevents the context menu from showing up when you right-click an image.
- JavaScript: You can also use JavaScript to change the right-click functionality.
- Plugins: If you’re running a WordPress site but aren’t tech-savvy, consider installing a plugin like Disable Right Click For WP to make the work easier.
9. Using Watermarks
Visible watermarking strongly discourages unauthorized image use. Unlike right-click limits that hamper sites, watermarks don’t impact performance. And they simplify proving infringement.
Here’s an example of a watermarked image:

How to Watermark Your Images
Adding watermarks is easy:
- Software solutions: You can opt for software like PhotoShop and LightRoom to add text or image watermarks by overlaying them on the image.
- Online tools: Free watermarking tools are available on the internet. These tools come with pre-designed logos and texts and are perfect for quick and easy solutions.
- Manual methods: Custom rubber stamps offer unique textures for physical image copies.
For best results, pair watermarking with complementary protections like metadata tagging.
10. Use Invisible On-Screen Barcodes
Invisible barcodes can encode contact data across image pixels, readable only by scanning software.
Barcodes survive editing and format changes, but their subtle nature requires reinforcement. Still, you’ll need to register the image and use it in tandem with visible watermark warnings.
Summary
Protecting your online photos doesn’t have to be a headache! Start by registering your work with the U.S. Copyright Office. This creates a clear record of ownership for anyone to see.
Add watermarks and hidden metadata to your images. These act like digital signatures, embedding your information directly into the files. Some platforms even allow the disablement of right-click downloads for an extra layer of defense.
Don’t just set it and forget it—use tools like Google Lens or other image-matching software to regularly search for unauthorized copies of your work. This way, you can catch and address any misuse.
FAQs
What is the right to protect images?
Protect your legal rights by ensuring your images are copyrighted. This prevents others from using them without your permission and allows you to take action if they do.
What is the best way to protect photos?
Use copyright to secure legal ownership and add watermarks to discourage unauthorized use. Backing up your photos and using metadata can also help prove ownership.
What does protect your image mean?
It means safeguarding your photos or digital images from unauthorized use, copying, or distribution. This can involve copyrighting, watermarking, or using tools to track and manage usage online.
What does protect images do?
It prevents unauthorized use, copying, or sharing of your photos. Protection measures like copyrighting and watermarking help maintain ownership and control over your work.